Difference between revisions of "CCNP SWITCH/Securing the Campus Infrastructure"
m (→VLAN Hopping) |
m (→VLAN Attacks) |
||
| Line 17: | Line 17: | ||
===VLAN Hopping=== | ===VLAN Hopping=== | ||
By altering the VLAN ID on packets encapsulated for trunking, an attacking device can send or receive packets on various VLANs, bypassing Layer 3 security measures.<br/> | By altering the VLAN ID on packets encapsulated for trunking, an attacking device can send or receive packets on various VLANs, bypassing Layer 3 security measures.<br/> | ||
| − | '''Mitigation'''<br/> | + | '''Mitigation:'''<br/> |
Tighten up trunk configurations and the negotiation state of unused ports. Place unused ports in a common VLAN. | Tighten up trunk configurations and the negotiation state of unused ports. Place unused ports in a common VLAN. | ||
===Attacks between devices on a common VLAN=== | ===Attacks between devices on a common VLAN=== | ||
Devices might need protection from one another, even though they are on a common VLAN. This is especially true on service-provider segments that support devices from multiple customers.<br/> | Devices might need protection from one another, even though they are on a common VLAN. This is especially true on service-provider segments that support devices from multiple customers.<br/> | ||
| − | '''Mitigation'''<br/> | + | '''Mitigation:'''<br/> |
Implement private VLANs (PVLAN). | Implement private VLANs (PVLAN). | ||
| + | |||
==Spoofing Attacks== | ==Spoofing Attacks== | ||
===DHCP starcation and spoofing=== | ===DHCP starcation and spoofing=== | ||
Revision as of 10:54, 2 September 2011
Contents
 This article is under development....
This article is under development....
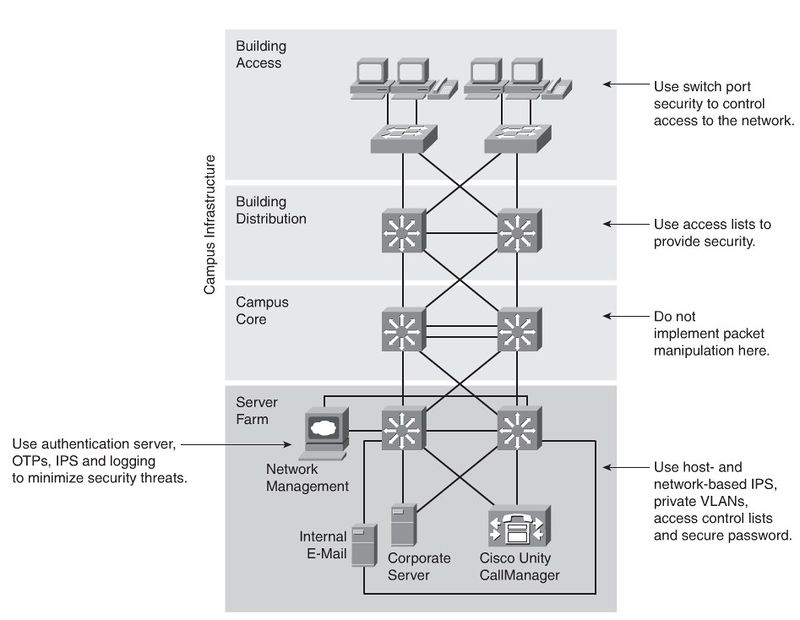
Securing the Campus Infrastructure
Security Infrastructure Services
Rouge Devices
Company employees sometimes plug inexpensive APs into company network devices to extend the network. But securing the wireless APs is not always a priority. Wired Rouge Devices could also be a problem, because of its nature.
Layer 2 Attack Categories
MAC Layer Attacks
MAC address flooding
Frames with unique, invalid source MAC addresses flood the switch, exhausting content addressable memory (CAM) table space, disallowing new entries from valid hosts. Traffic to valid hosts is subsequently flooded out all ports.
Mitigation:
Port security. MAC address VLAN access maps.
VLAN Attacks
VLAN Hopping
By altering the VLAN ID on packets encapsulated for trunking, an attacking device can send or receive packets on various VLANs, bypassing Layer 3 security measures.
Mitigation:
Tighten up trunk configurations and the negotiation state of unused ports. Place unused ports in a common VLAN.
Attacks between devices on a common VLAN
Devices might need protection from one another, even though they are on a common VLAN. This is especially true on service-provider segments that support devices from multiple customers.
Mitigation:
Implement private VLANs (PVLAN).