Difference between revisions of "CCNP 3 Minimizing Service Loss and Data Theft in a Campus Network"
m (→Configuring DHCP Snooping) |
m (→Describing Vulnerabilities in CDP) |
||
| Line 156: | Line 156: | ||
=Securing Network Switches= | =Securing Network Switches= | ||
==Describing Vulnerabilities in CDP== | ==Describing Vulnerabilities in CDP== | ||
| + | {| | ||
| + | |[[Image:ScreenShot581.jpg|800px|left|thumb|CDP Attack]] | ||
| + | |} | ||
| + | ==Telnet Protocol Vulnerabilities== | ||
| + | {| | ||
| + | |[[Image:ScreenShot582.jpg|800px|left|thumb|Telnet attach]] | ||
| + | |} | ||
| + | ==Configuring the Secure Shell Protocol== | ||
| + | {| | ||
| + | |[[Image:ScreenShot583.jpg|800px|left|thumb|SSH]] | ||
| + | |} | ||
| + | <source lang=cli> | ||
| + | Switch(config)# username Joe password User | ||
| + | Switch(config)# ip domain-name sshtest.lab | ||
| + | Switch(config)# crypto key generate key | ||
| + | Switch(config)# line vty 0 15 | ||
| + | Switch(config-line)# login local | ||
| + | Switch(config-line)# transport input ssh | ||
| + | </source> | ||
Revision as of 16:08, 15 September 2010
Contents
- 1 Understanding Switch Security Issues
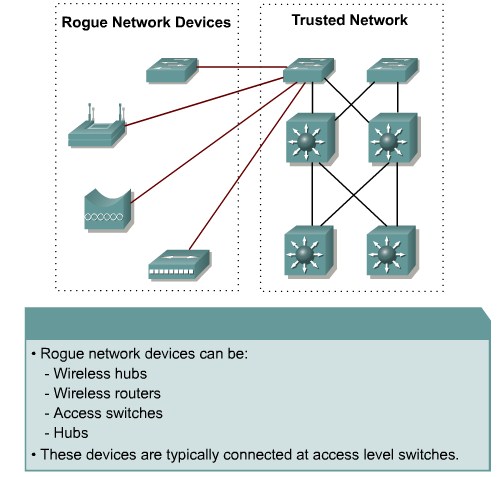
- 1.1 Describing Unauthorized Access by Rogue Devices
- 1.2 Switch Attack Categories
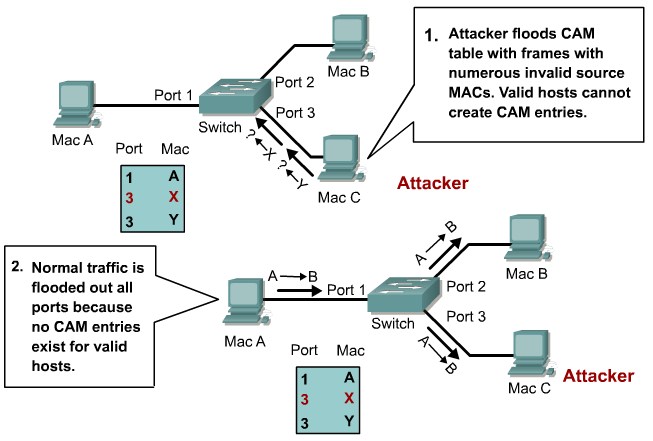
- 1.3 Describing a MAC Flooding Attack
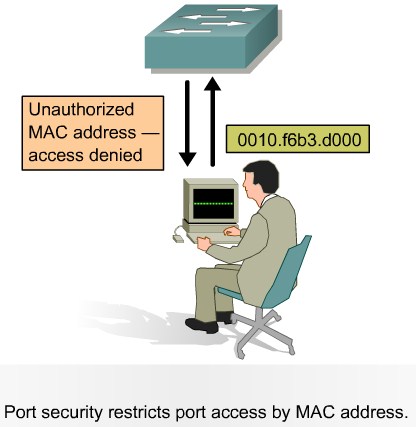
- 1.4 Describing Port Security
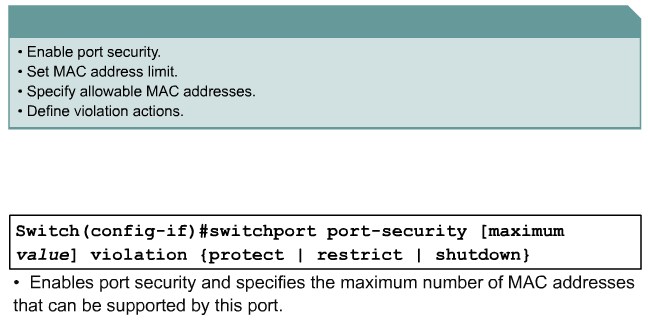
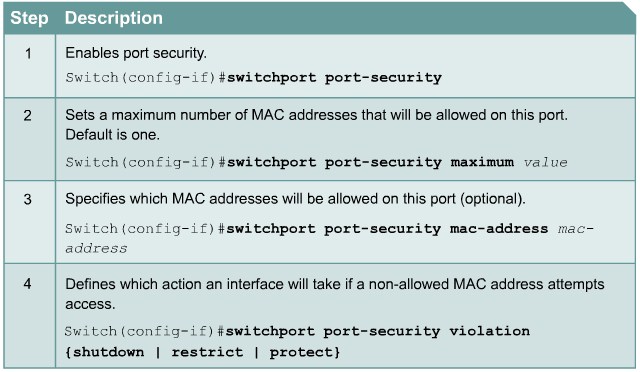
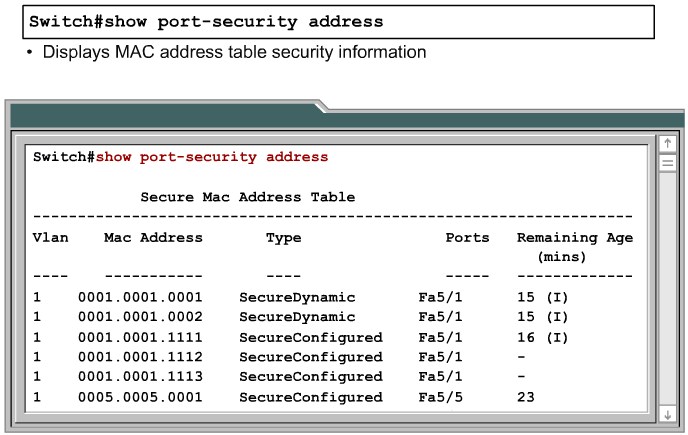
- 1.5 Configuring Port Security on a Switch
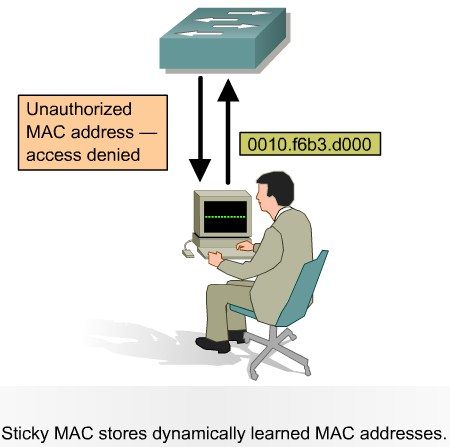
- 1.6 Port Security with Sticky MAC Addresses
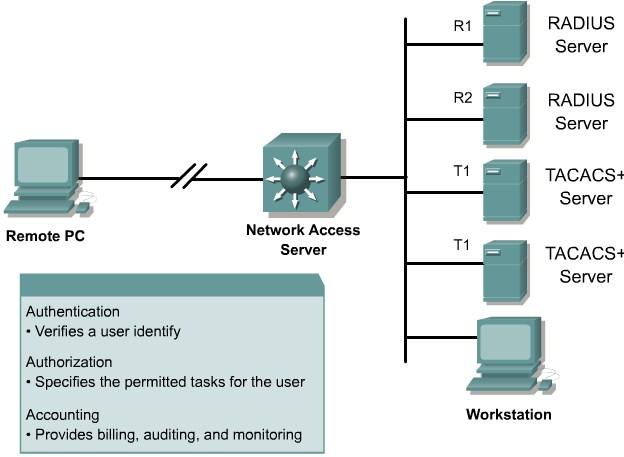
- 1.7 Authentication, Authorization, and Accounting
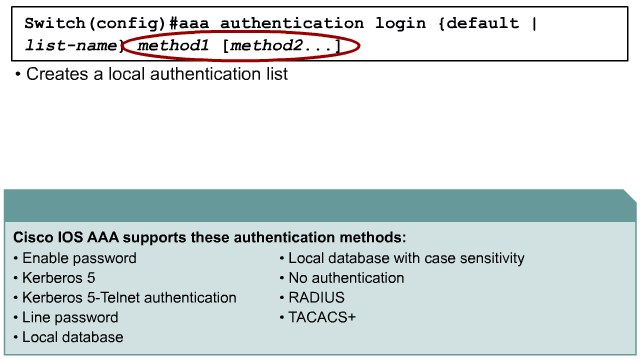
- 1.8 Authentication Methods
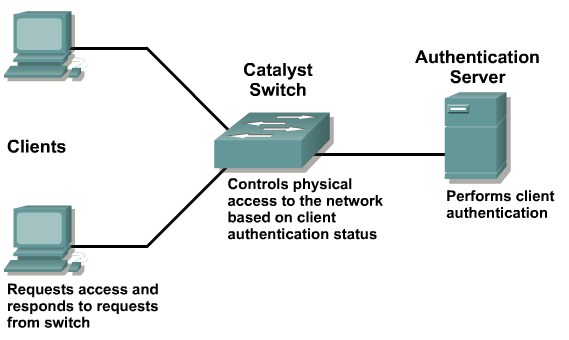
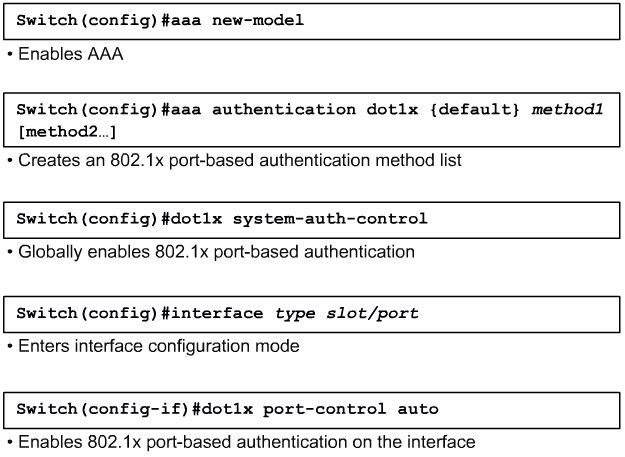
- 1.9 802.1x Port-Based Authentication
- 2 Protecting Against VLAN Attacks
- 3 Protecting Against Spoof Attacks
- 4 STP Security Mechanisms
- 5 Preventing STP Forwarding Loops
- 6 Securing Network Switches
Understanding Switch Security Issues
Describing Unauthorized Access by Rogue Devices
Switch Attack Categories
- MAC layer attacks
- VLAN attacks
- Spoof attacks
- Switch device attacks
| MAC address Flooding | Port Security |
| VLAN Hooping | Tighten up trunk configurations and the nogotiation state |
| Attacks between devices on a common VLAN | Implement Private VLANS(PVLANs) |
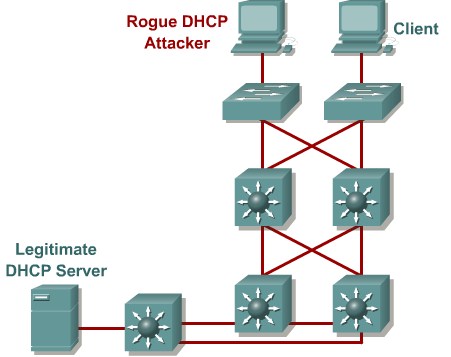
| DHCP Spoofing | USe DHCP Snooping |
| Spanning tree compromises | Proactively configure the primary and backup root devices, Enable root guard |
| MAC Spoofing | Use DHCP Snooping. Port security. |
| ARP Spoofing | Use Dynamic ARP Inspection. DHCP Snooping, Port Security |
| CDP Manipulation | Diable CDP on al ports where it is not intentionally used. |
| SSH & Telnet attacks | Use SSHv2. Use Telnet with VTY ACLs |
Describing a MAC Flooding Attack
Describing Port Security
Configuring Port Security on a Switch
|
Protect: Frames from the non-allowed address are dropped, but there is no log of the violation. |
Port Security with Sticky MAC Addresses
Authentication, Authorization, and Accounting
Authentication Methods
802.1x Port-Based Authentication
|
force-authorized: Disables 802.1x port-based authentication and causes the port to transition to the authorized state without any authentication exchange required. The port transmits and receives normal traffic without 802.1x-based authentication of the client. This is the default setting. |
Protecting Against VLAN Attacks
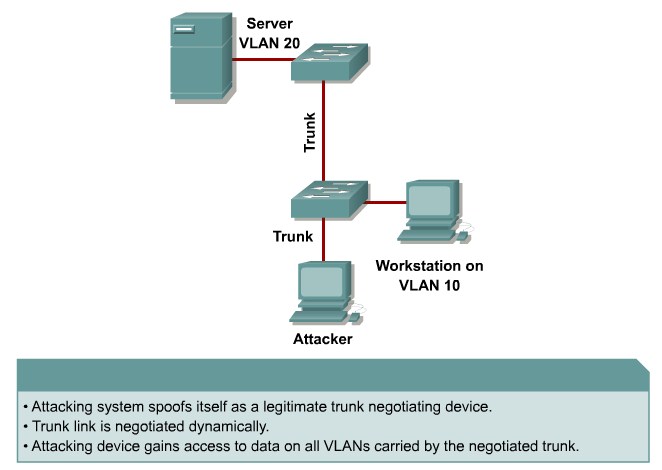
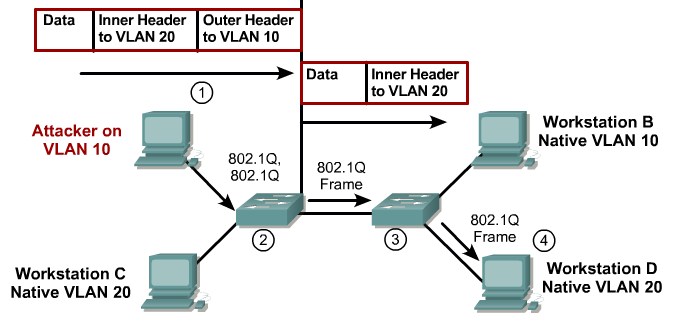
Explaining VLAN Hopping
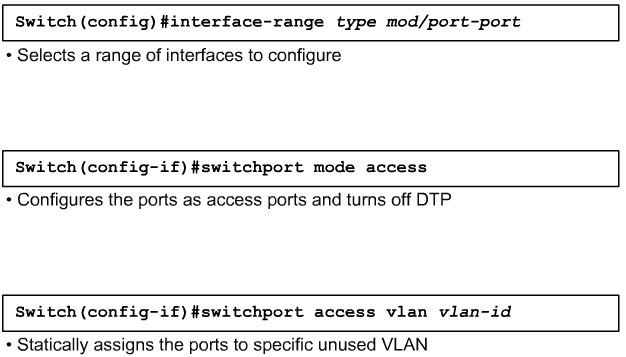
Mitigating VLAN Hopping
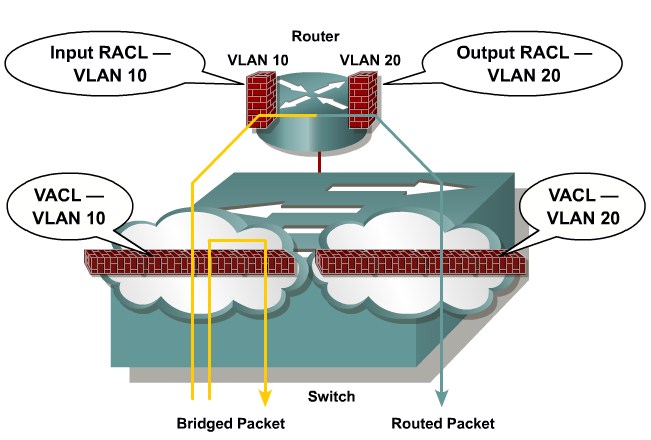
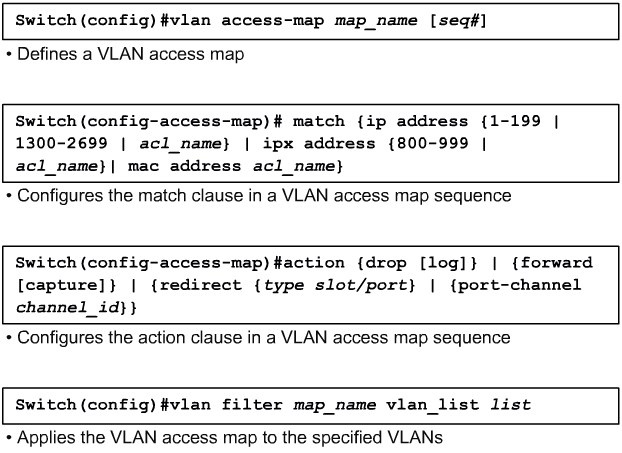
VLAN Access Control Lists
Configuring VACLs
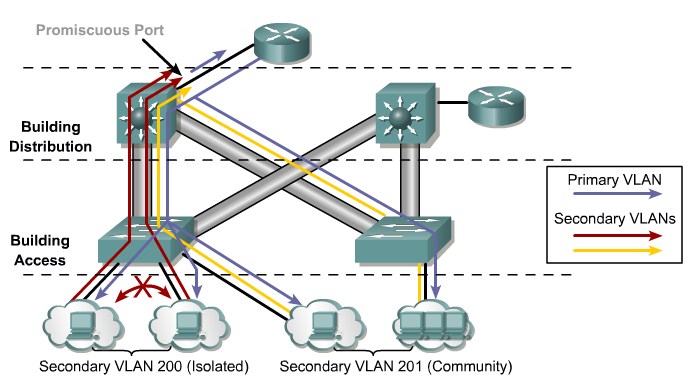
Private VLANs and Protected Ports
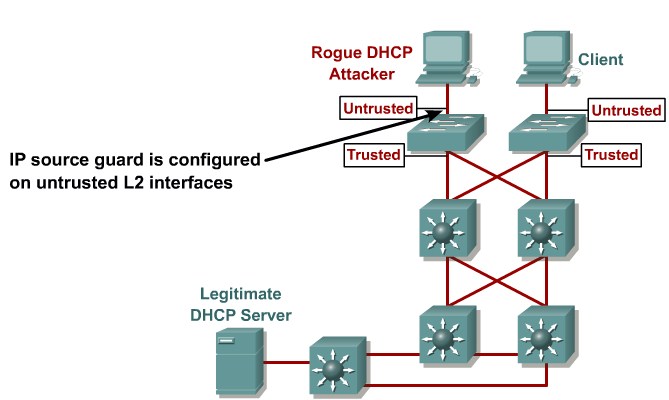
Protecting Against Spoof Attacks
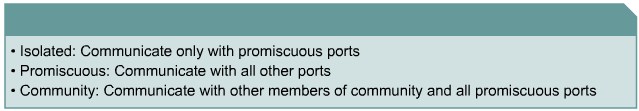
Describing a DHCP Spoof Attack
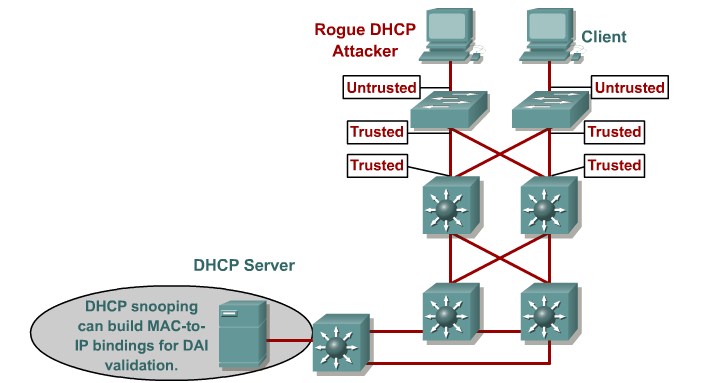
Describing DHCP Snooping
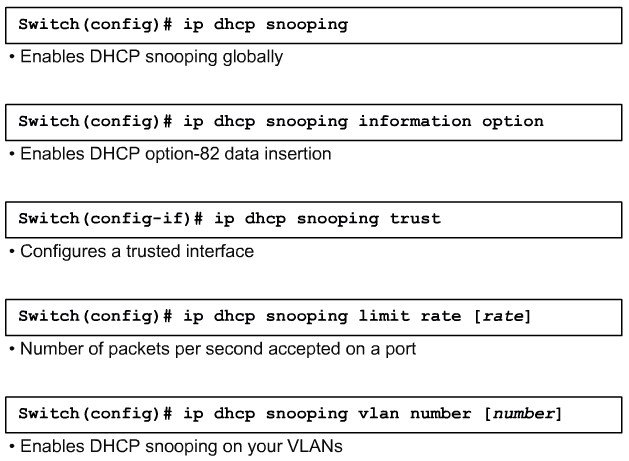
Configuring DHCP Snooping
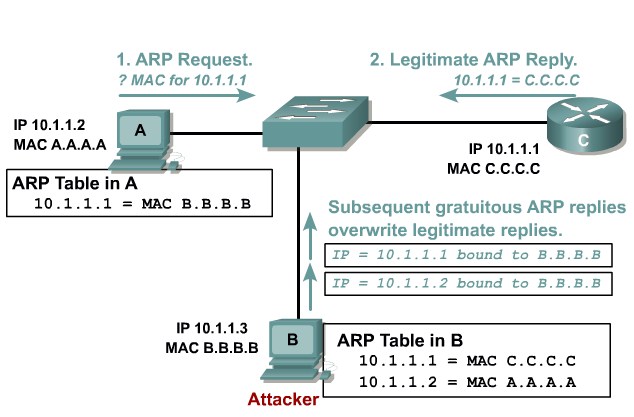
Describing ARP Spoofing
Dynamic ARP Inspection
STP Security Mechanisms
Protecting the Operation of STP
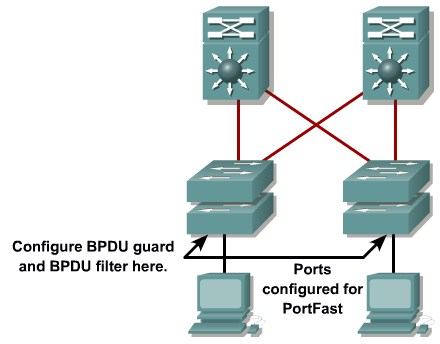
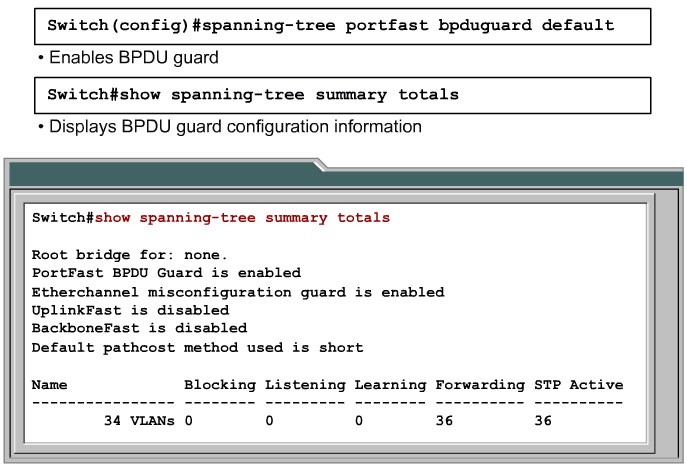
Configuring BPDU Guard
Configuring BPDU Filtering
STP Root Guard
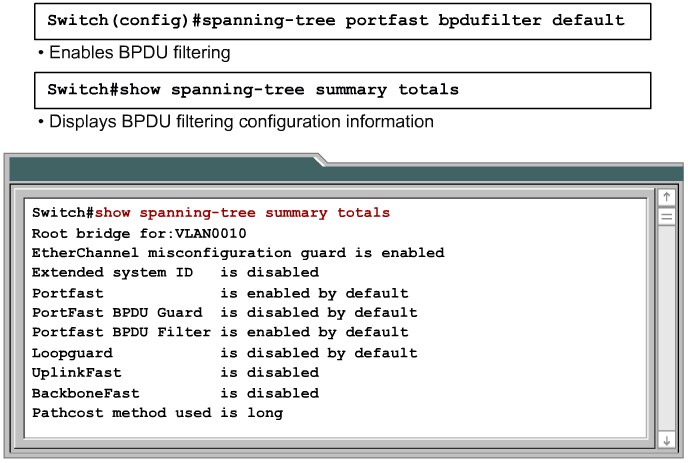
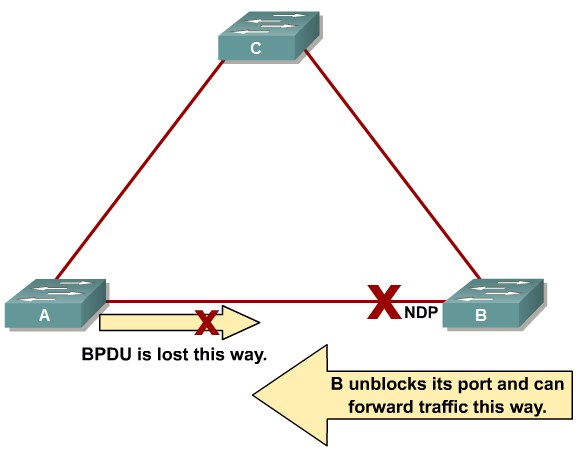
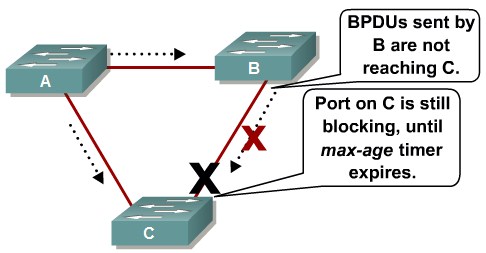
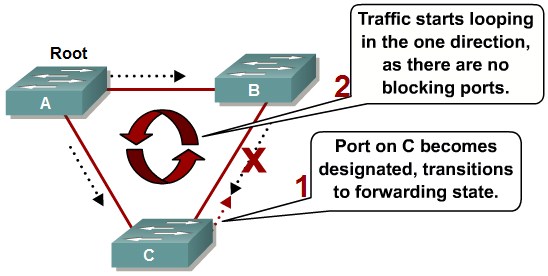
Preventing STP Forwarding Loops
Unidirectional Link Detection
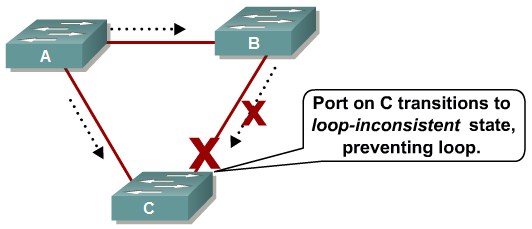
Loop Guard
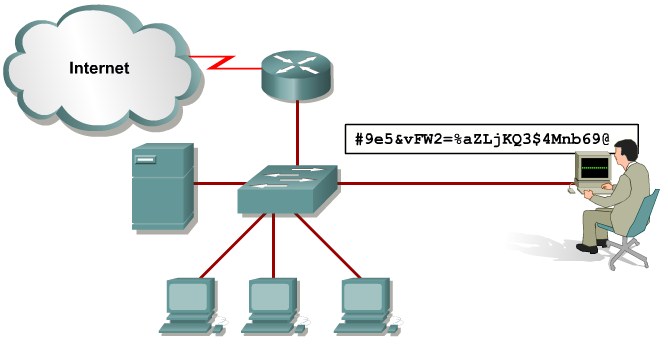
Comparing Loop Guard and UDLD
Securing Network Switches
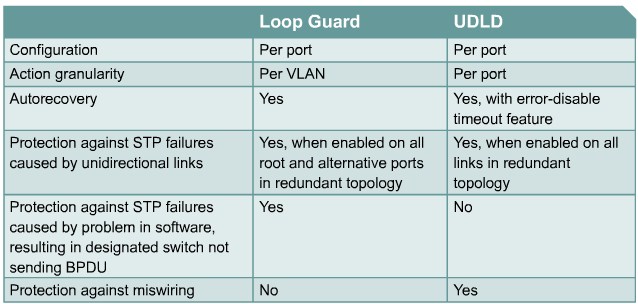
Describing Vulnerabilities in CDP
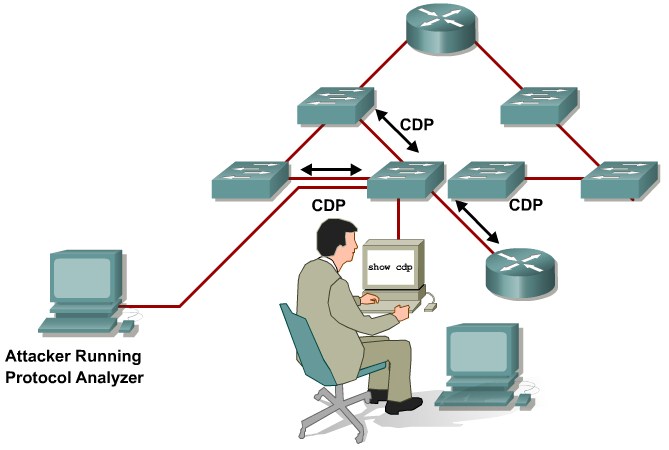
Telnet Protocol Vulnerabilities
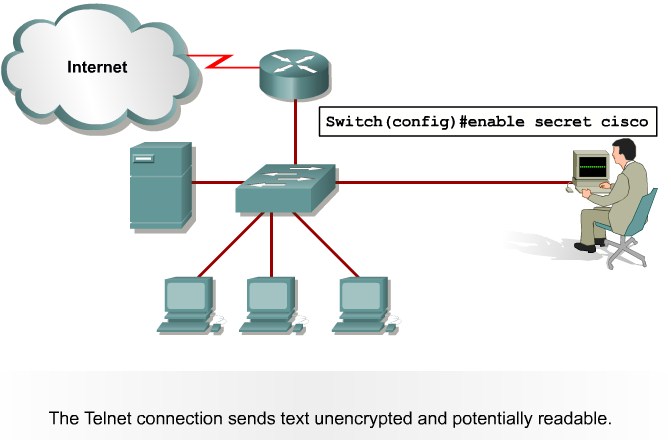
Configuring the Secure Shell Protocol
Switch(config)# username Joe password User
Switch(config)# ip domain-name sshtest.lab
Switch(config)# crypto key generate key
Switch(config)# line vty 0 15
Switch(config-line)# login local
Switch(config-line)# transport input ssh