Difference between revisions of "CCNP 3 Minimizing Service Loss and Data Theft in a Campus Network"
m (→Describing a MAC Flooding Attack) |
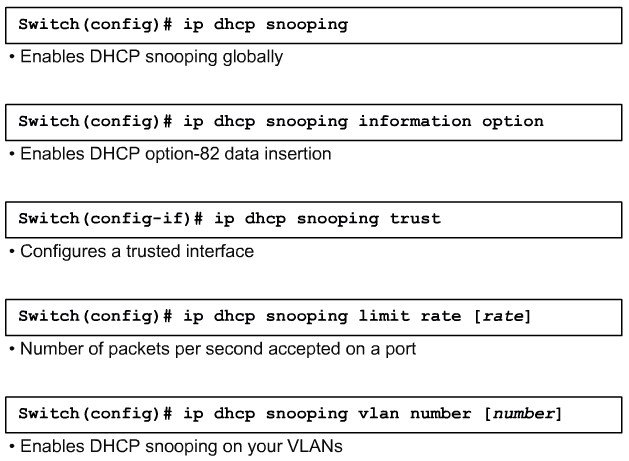
m (→Configuring DHCP Snooping) |
||
| Line 109: | Line 109: | ||
{| | {| | ||
|[[Image:ScreenShot568.jpg|800px|left|thumb|DHCP Snooping]] | |[[Image:ScreenShot568.jpg|800px|left|thumb|DHCP Snooping]] | ||
| + | |- | ||
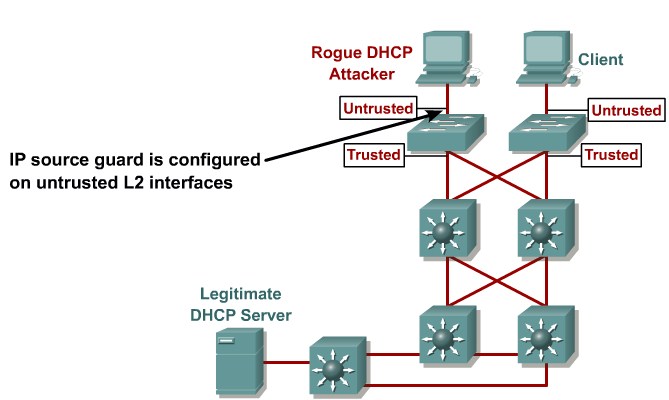
| + | |[[Image:ScreenShot569.jpg|800px|left|thumb|IP Source Guard]] | ||
|} | |} | ||
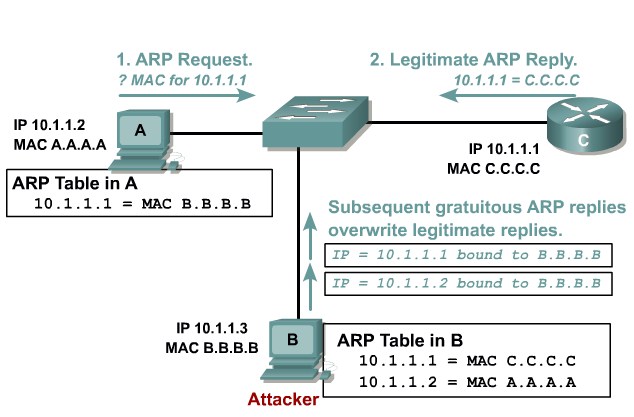
| + | ==Describing ARP Spoofing== | ||
| + | {| | ||
| + | |[[Image:ScreenShot570.jpg|800px|left|thumb|ARP Spoofing]] | ||
| + | |} | ||
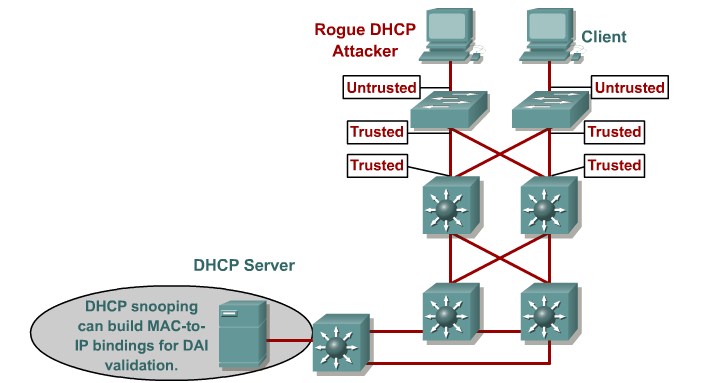
| + | ==Dynamic ARP Inspection== | ||
| + | {| | ||
| + | |[[Image:ScreenShot571.jpg|800px|left|thumb|DAI]] | ||
| + | |} | ||
| + | =STP Security Mechanisms= | ||
| + | ==Protecting the Operation of STP== | ||
| + | {| | ||
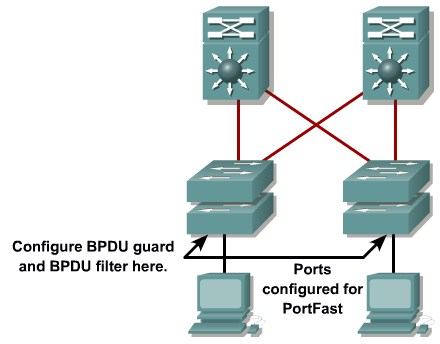
| + | |[[Image:ScreenShot572.jpg|800px|left|thumb|Portfast protection]] | ||
| + | |} | ||
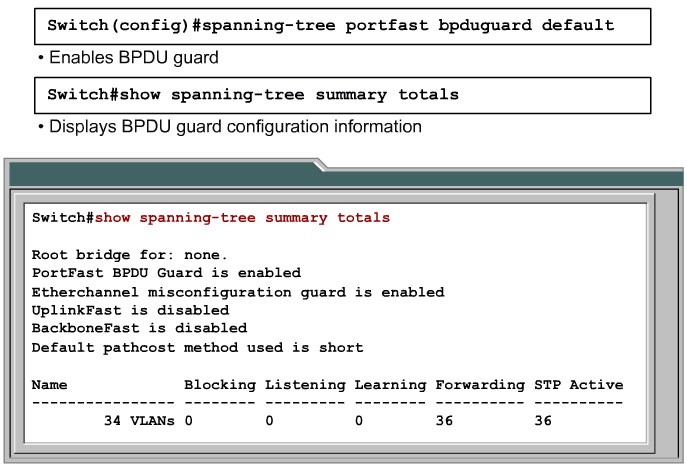
| + | ==Configuring BPDU Guard== | ||
| + | {| | ||
| + | |[[Image:ScreenShot573.jpg|800px|left|thumb|Enabling and Verifying BPDY Guard]] | ||
| + | |} | ||
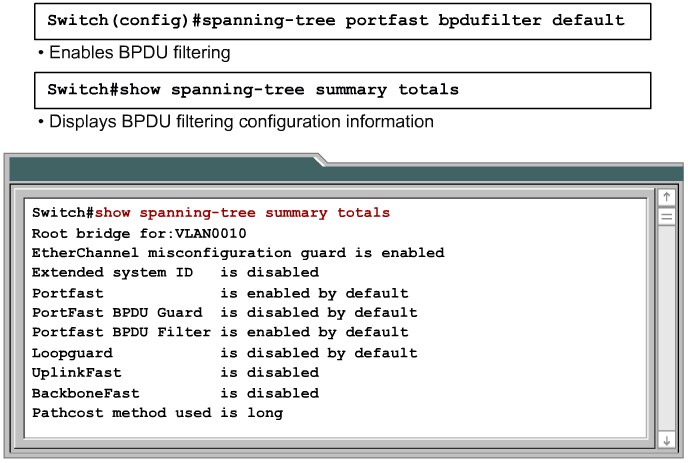
| + | ==Configuring BPDU Filtering== | ||
| + | {| | ||
| + | |[[Image:ScreenShot574.jpg|800px|left|thumb|BPDu Filtering]] | ||
| + | |} | ||
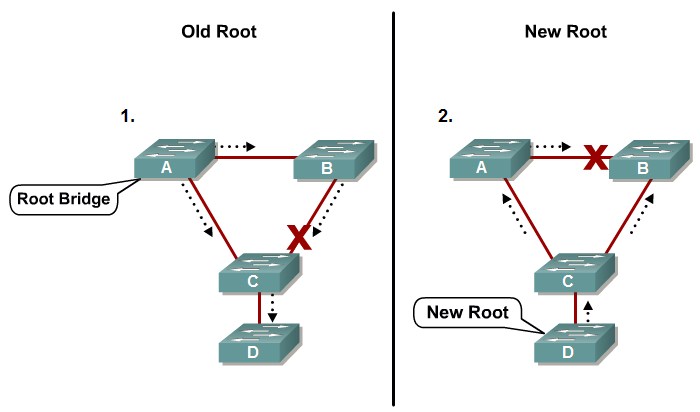
| + | ==STP Root Guard== | ||
| + | {| | ||
| + | |[[Image:ScreenShot575.jpg|800px|left|thumb|STP Root Guard]] | ||
| + | |} | ||
| + | =Preventing STP Forwarding Loops= | ||
| + | ==Unidirectional Link Detection== | ||
| + | {| | ||
| + | |[[Image:ScreenShot576.jpg|800px|left|thumb|UDLD]] | ||
| + | |} | ||
| + | ==Loop Guard== | ||
| + | {| | ||
| + | |[[Image:ScreenShot577.jpg|800px|left|thumb|Loop Guard]] | ||
| + | |- | ||
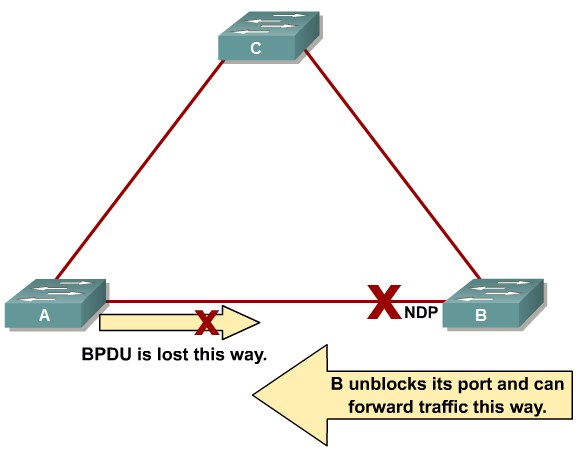
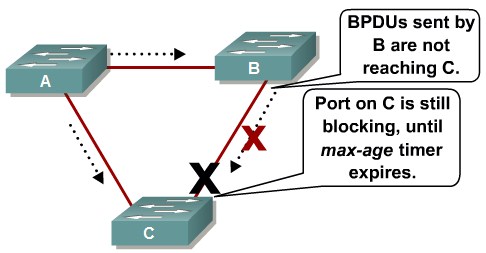
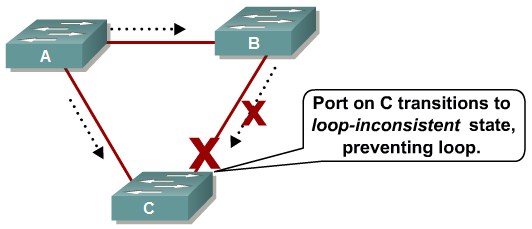
| + | |[[Image:ScreenShot578.jpg|800px|left|thumb|Before Loop Guard]] | ||
| + | |- | ||
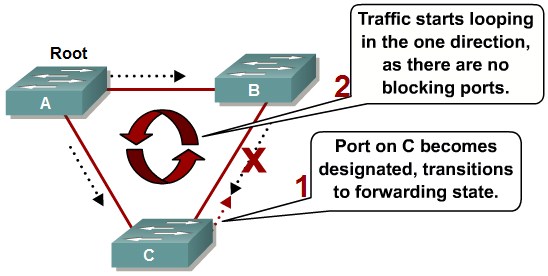
| + | |[[Image:ScreenShot579.jpg|800px|left|thumb|With Loop Guard]] | ||
| + | |} | ||
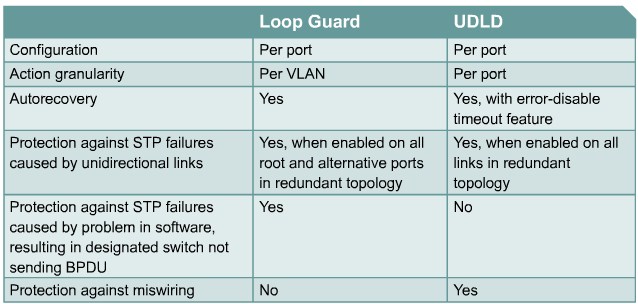
| + | ==Comparing Loop Guard and UDLD== | ||
| + | {| | ||
| + | |[[Image:ScreenShot580.jpg|800px|left|thumb|]] | ||
| + | |} | ||
| + | =Securing Network Switches= | ||
| + | ==Describing Vulnerabilities in CDP== | ||
Revision as of 16:04, 15 September 2010
Contents
- 1 Understanding Switch Security Issues
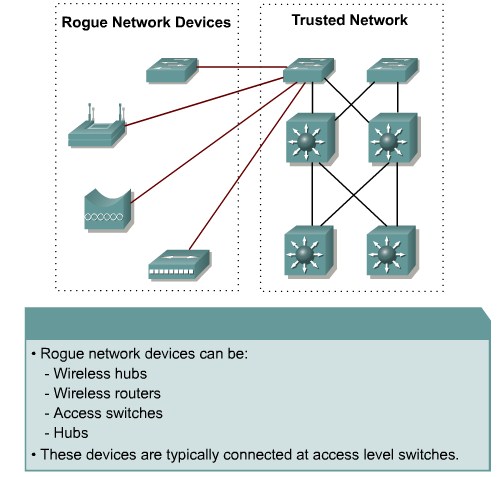
- 1.1 Describing Unauthorized Access by Rogue Devices
- 1.2 Switch Attack Categories
- 1.3 Describing a MAC Flooding Attack
- 1.4 Describing Port Security
- 1.5 Configuring Port Security on a Switch
- 1.6 Port Security with Sticky MAC Addresses
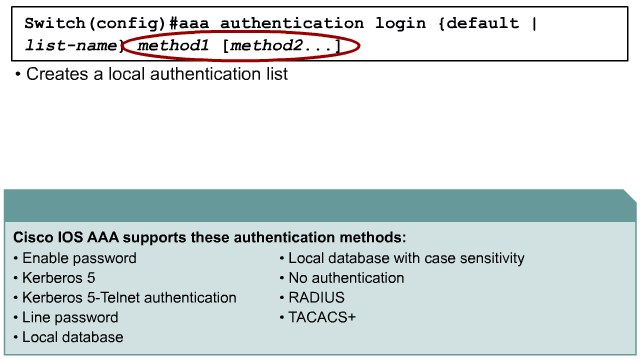
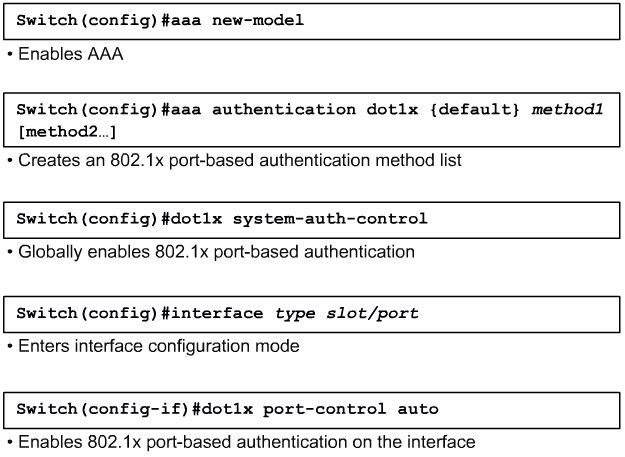
- 1.7 Authentication, Authorization, and Accounting
- 1.8 Authentication Methods
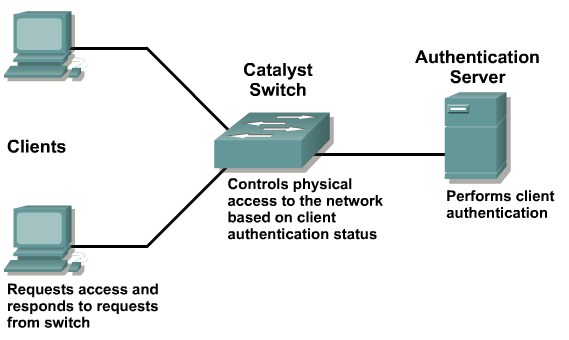
- 1.9 802.1x Port-Based Authentication
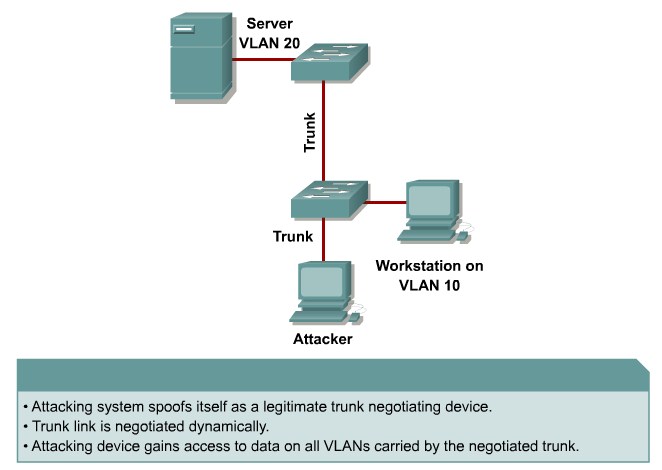
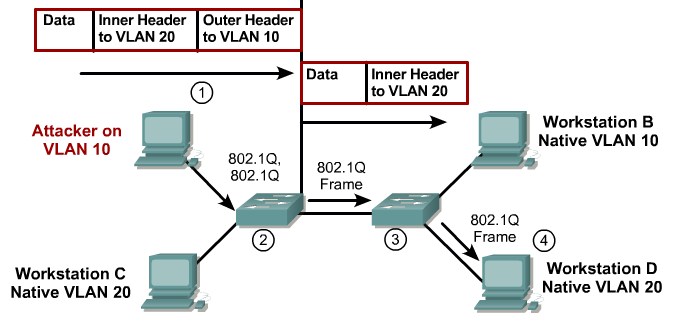
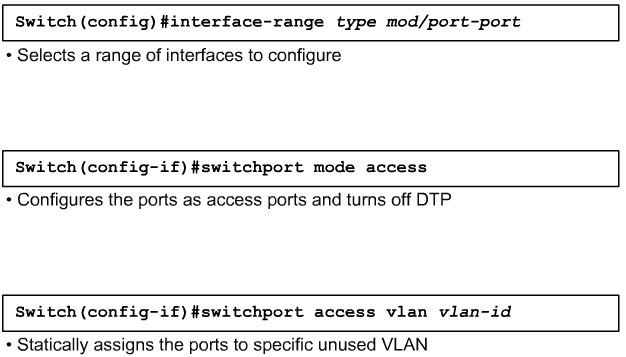
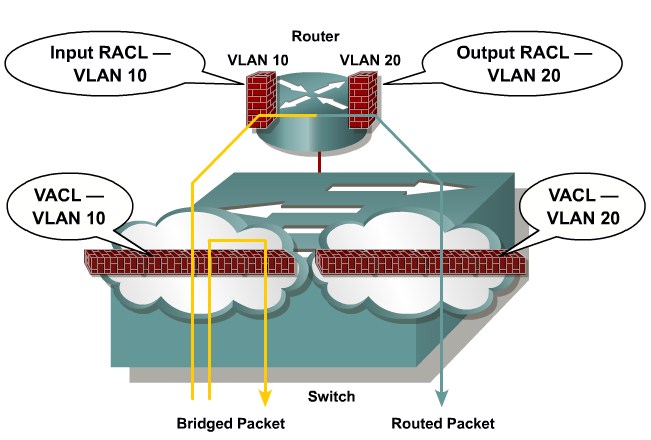
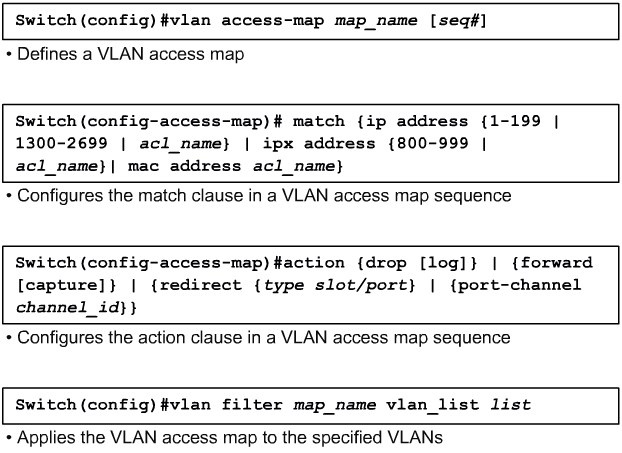
- 2 Protecting Against VLAN Attacks
- 3 Protecting Against Spoof Attacks
- 4 STP Security Mechanisms
- 5 Preventing STP Forwarding Loops
- 6 Securing Network Switches
Understanding Switch Security Issues
Describing Unauthorized Access by Rogue Devices
Switch Attack Categories
- MAC layer attacks
- VLAN attacks
- Spoof attacks
- Switch device attacks
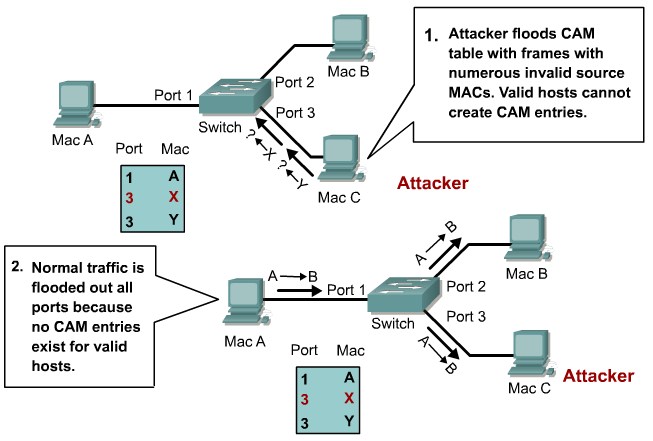
| MAC address Flooding | Port Security |
| VLAN Hooping | Tighten up trunk configurations and the nogotiation state |
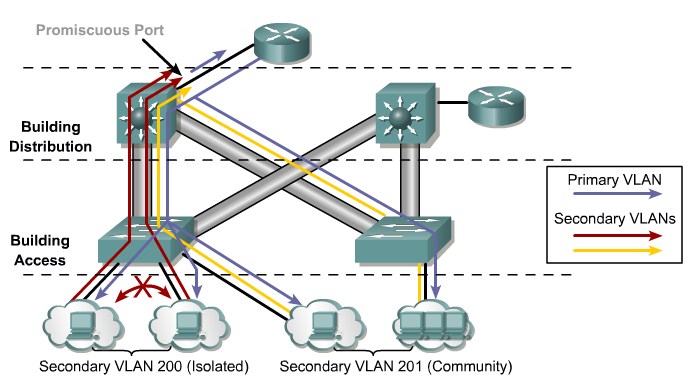
| Attacks between devices on a common VLAN | Implement Private VLANS(PVLANs) |
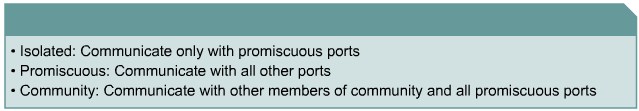
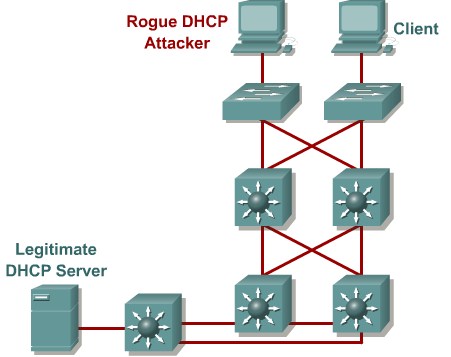
| DHCP Spoofing | USe DHCP Snooping |
| Spanning tree compromises | Proactively configure the primary and backup root devices, Enable root guard |
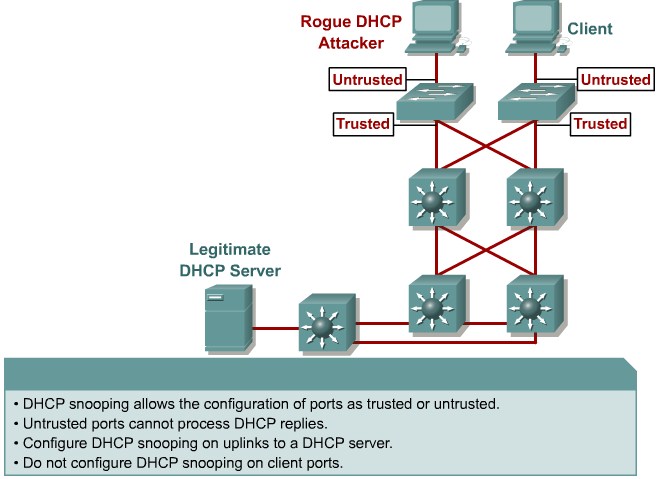
| MAC Spoofing | Use DHCP Snooping. Port security. |
| ARP Spoofing | Use Dynamic ARP Inspection. DHCP Snooping, Port Security |
| CDP Manipulation | Diable CDP on al ports where it is not intentionally used. |
| SSH & Telnet attacks | Use SSHv2. Use Telnet with VTY ACLs |
Describing a MAC Flooding Attack
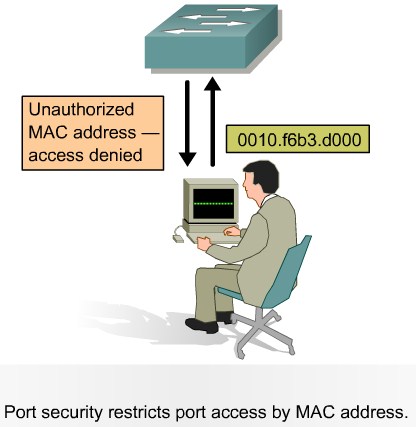
Describing Port Security
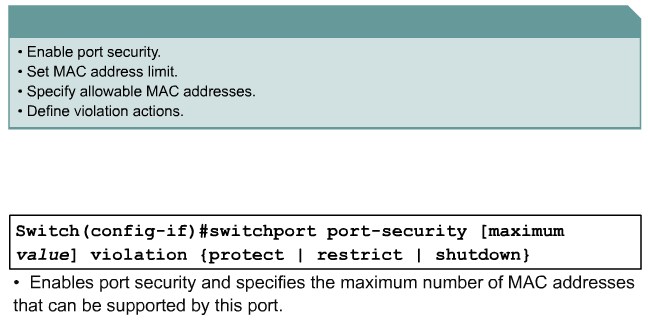
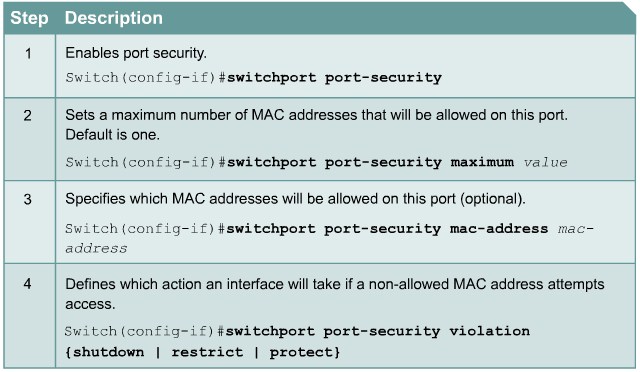
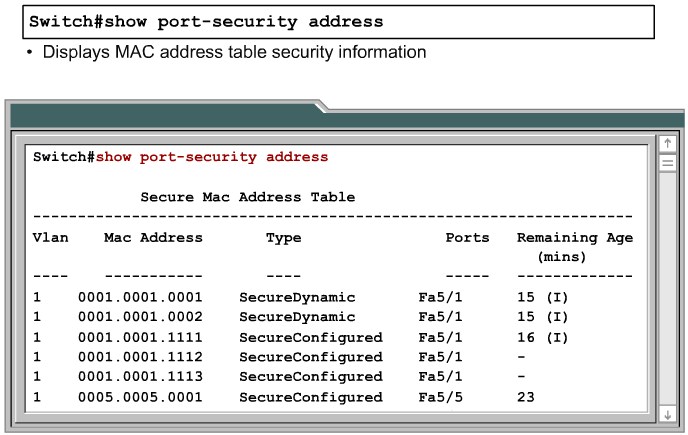
Configuring Port Security on a Switch
|
Protect: Frames from the non-allowed address are dropped, but there is no log of the violation. |
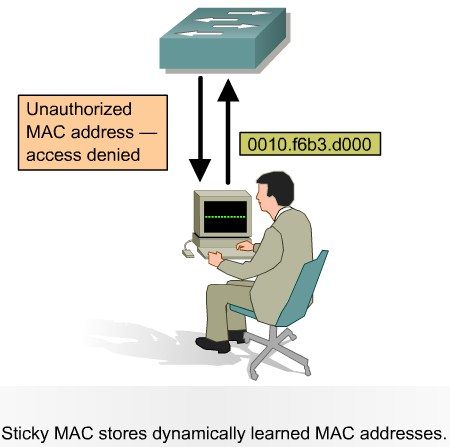
Port Security with Sticky MAC Addresses
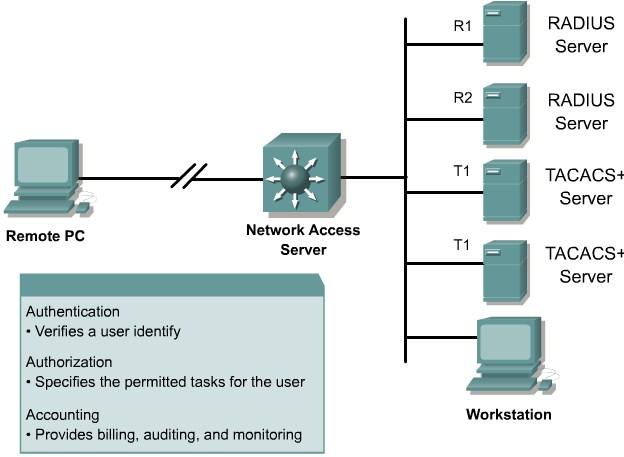
Authentication, Authorization, and Accounting
Authentication Methods
802.1x Port-Based Authentication
|
force-authorized: Disables 802.1x port-based authentication and causes the port to transition to the authorized state without any authentication exchange required. The port transmits and receives normal traffic without 802.1x-based authentication of the client. This is the default setting. |