Netband Project - IOS firewall
From Teknologisk videncenter
<accesscontrol>NetBand</accesscontrol> This page is part of the Netband Project
Contents
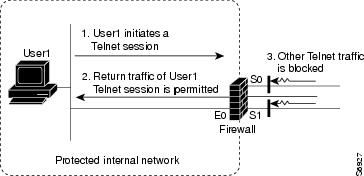
Context Based Access Control (CBAC)
- filters TCP and UDP packets based on application-layer protocol session information.
- more flexible than access control lists, that checks packets at the network layer, or at most, the transport layer
- inspects packet sequence numbers in TCP connections
- detects unusually high rates of new connections and issue alert messages.
- creates temporary openings in the return acl to allow traffic back in.
Configuration
- Note: The router only keeps track of the configured protocols
ip inspect audit-trail ip inspect name iosfw ftp ip inspect name iosfw tcp ip inspect name iosfw udp ip inspect name iosfw http ip inspect name iosfw https ! interface FastEthernet0/0 description OUTSIDE ip inspect iosfw out ip access-group 101 in ! access-list 101 permit udp any eq isakmp any eq isakmp access-list 101 permit esp any any access-list 101 permit tcp any any eq 22 access-list 101 deny ip any any log
Verification
B1rt1#sh ip inspect sessions Established Sessions Session 65E14830 (10.2.1.10:3935)=>(195.137.194.128:80) http SIS_OPEN Session 65E15310 (10.2.1.10:3936)=>(195.137.194.128:80) http SIS_OPEN Session 65E15058 (10.2.1.10:3937)=>(195.137.194.128:80) http SIS_OPEN Session 65E155C8 (10.2.1.10:3934)=>(195.137.194.128:80) http SIS_OPEN
- Syslog audit trail
Apr 27 10:22:06.521: %FW-6-SESS_AUDIT_TRAIL_START: Start http session: initiator (10.2.1.10:3898) -- responder (195.137.194.128:80) Apr 27 10:22:18.044: %FW-6-SESS_AUDIT_TRAIL: Stop http session: initiator (10.2.1.10:3898) sent 1247 bytes -- responder (195.137.194.128:80) sent 144791 bytes