Difference between revisions of "CCNA Explorer 3 Basic Switch Concepts and Configuration"
From Teknologisk videncenter
m |
m |
||
| (5 intermediate revisions by 2 users not shown) | |||
| Line 105: | Line 105: | ||
|[[Image:ScreenShot066.jpg|800px|left|thumb|EXEC mode password]] | |[[Image:ScreenShot066.jpg|800px|left|thumb|EXEC mode password]] | ||
|- | |- | ||
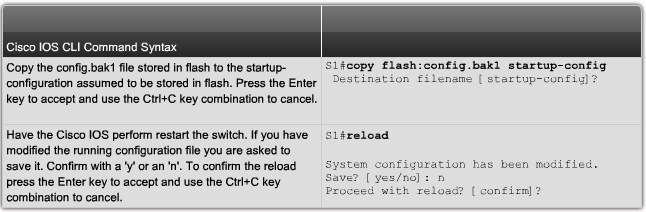
| − | |[[Image: | + | |[[Image:ScreenShot1061.jpg|800px|left|thumb|Configure encypted passwords]] |
|- | |- | ||
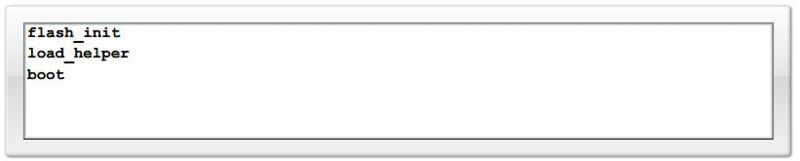
|[[Image:ScreenShot001.jpg|800px|left|thumb|Password recovery]] | |[[Image:ScreenShot001.jpg|800px|left|thumb|Password recovery]] | ||
| Line 120: | Line 120: | ||
|- | |- | ||
| | | | ||
| + | Hvad med '''aaa new-model''' & '''username cisco password cisco''' | ||
==Common Security Attacks== | ==Common Security Attacks== | ||
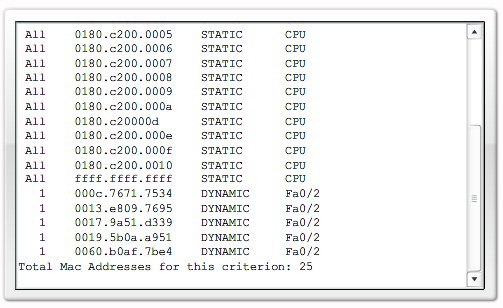
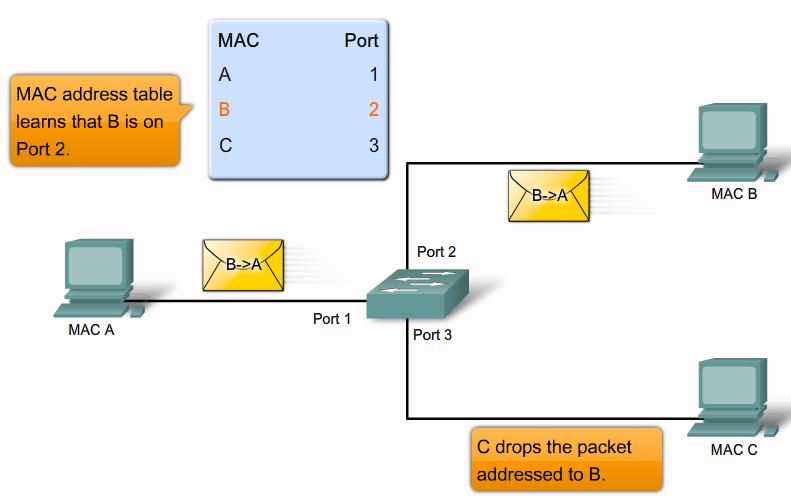
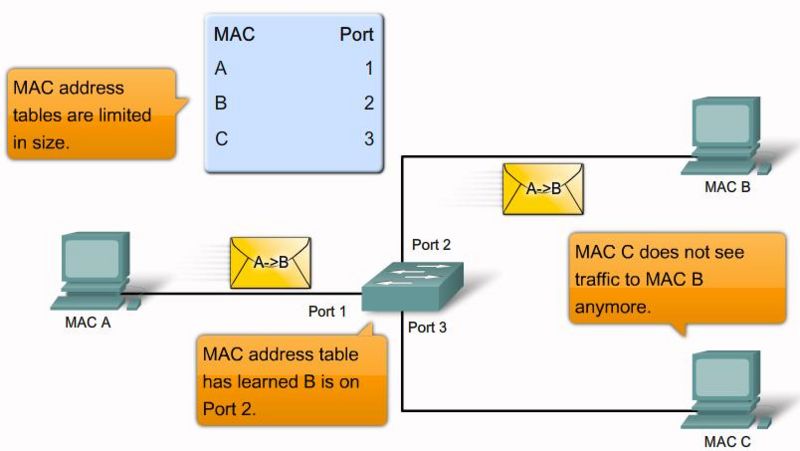
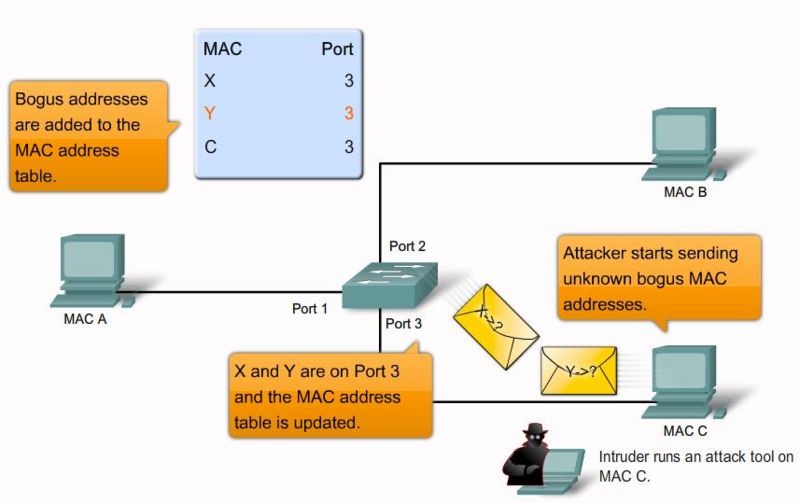
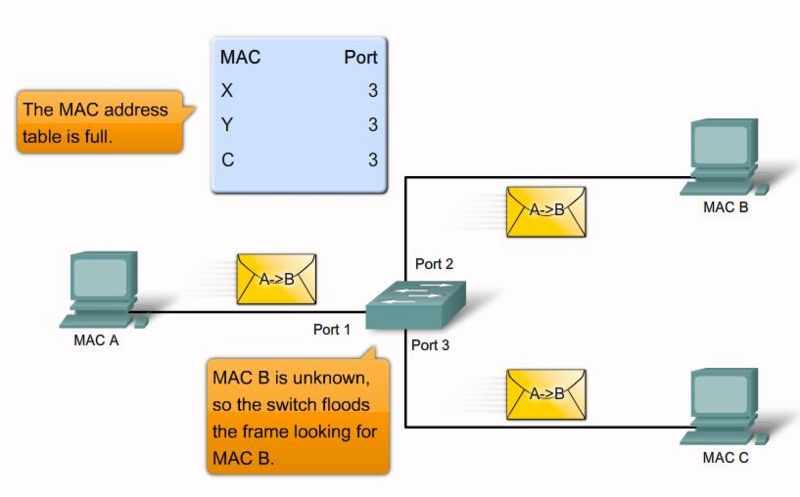
===MAC Address Flooding=== | ===MAC Address Flooding=== | ||
| Line 132: | Line 133: | ||
|- | |- | ||
|[[Image:ScreenShotNew010.jpg|800px|left|thumb|MAC flooding attack step 5]] | |[[Image:ScreenShotNew010.jpg|800px|left|thumb|MAC flooding attack step 5]] | ||
| − | | | + | |} |
| − | + | [http://www.cisco.com/en/US/docs/switches/lan/catalyst3750/software/release/12.2_25_see/configuration/guide/swsdm.html SDM Templates] | |
| + | |||
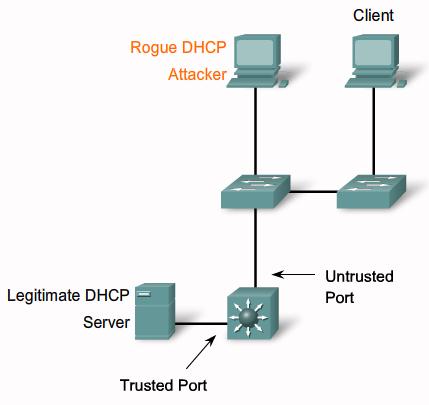
===DHCP Spoofing=== | ===DHCP Spoofing=== | ||
{| | {| | ||
| Line 151: | Line 153: | ||
|- | |- | ||
|[[Image:ScreenShotNew017.jpg|800px|left|thumb|Secure Unused Ports]] | |[[Image:ScreenShotNew017.jpg|800px|left|thumb|Secure Unused Ports]] | ||
| − | |- | + | |} |
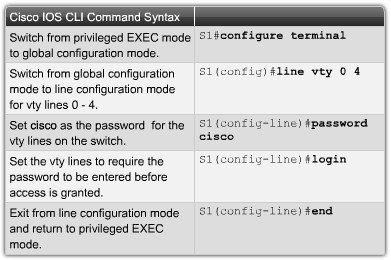
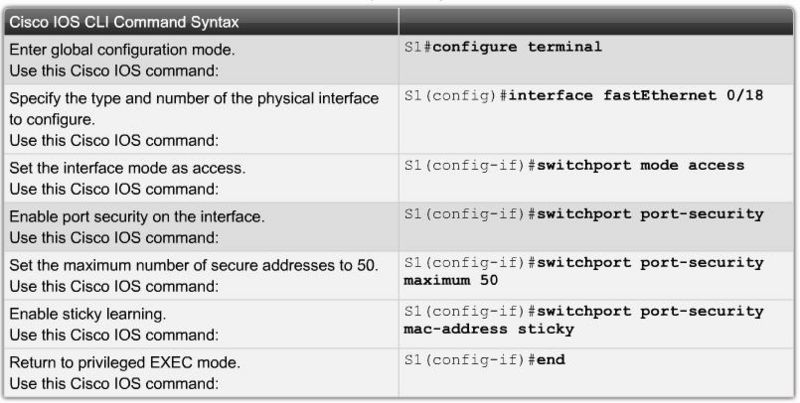
| − | + | '''Security Violation Modes''' | |
| + | *'''Protect''': When the number of secure MAC addresses reaches the limit allowed on the port, packets with unknown source addresses are dropped. | ||
| + | *'''Restrict''': When the number of secure MAC addresses reaches the limit allowed on the port, packets with unknown source addresses are dropped. A SNMP trap is sent, a syslog message is logged, and the violation counter increments. | ||
| + | *'''Shutdown'''(Default<ref>http://www.cisco.com/en/US/docs/switches/lan/catalyst6500/ios/12.2SX/configuration/guide/port_sec.html#wp1038518</ref>): In this mode, a port security violation causes the interface to immediately become error-disabled and turns off the port LED. It also sends an SNMP trap, logs a syslog message. | ||
| + | =References= | ||
| + | <references/> | ||
Latest revision as of 10:00, 7 August 2013
| ||||||||||||||||||||||||||||||||||||||||||||||||
| ||||||||||||||||||||||||||||||||||||||||||||||||
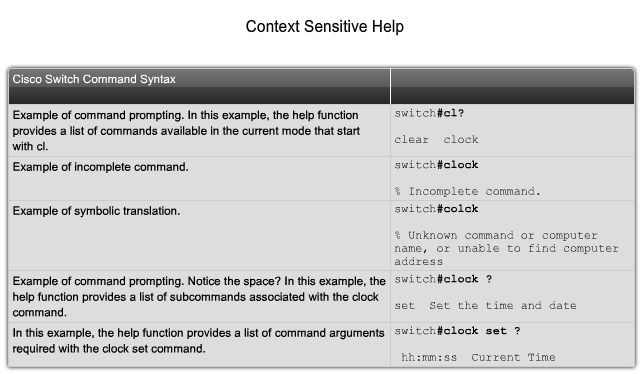
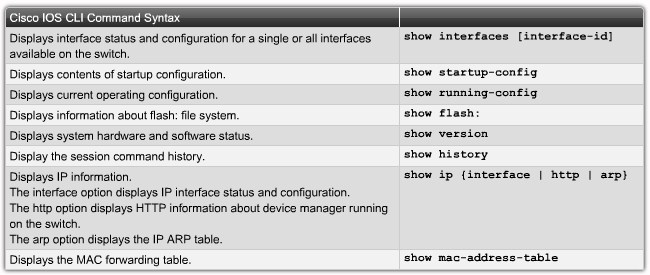
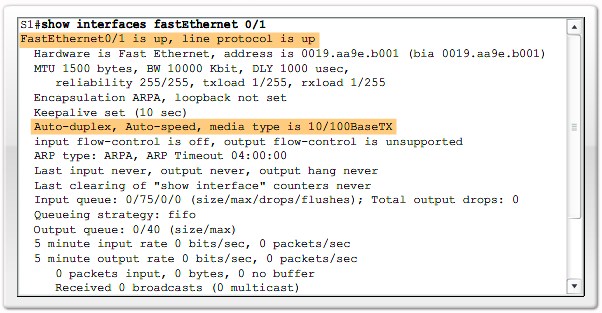
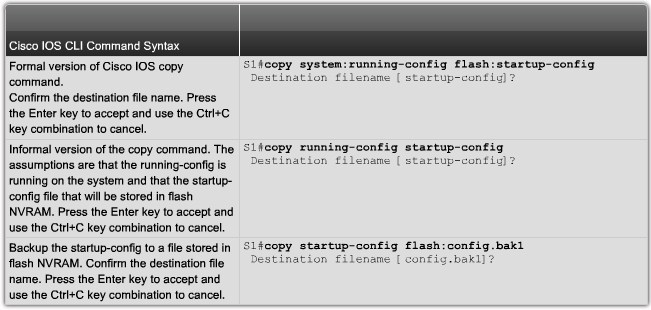
ContentsNavigating Command-Line Interfaces Modes
|