Difference between revisions of "Iptables"
From Teknologisk videncenter
m (→Using IPTABLES) |
m |
||
| Line 2: | Line 2: | ||
== Using IPTABLES == | == Using IPTABLES == | ||
Iptables is a commandline command with numerous options, and need some training to master. | Iptables is a commandline command with numerous options, and need some training to master. | ||
| − | + | There are three tables you can use filter(default) [[NAT_Linux|nat]] and mangle. Only filter and [[NAT_Linux|nat]] shown below. | |
| − | |||
| − | |||
| − | |||
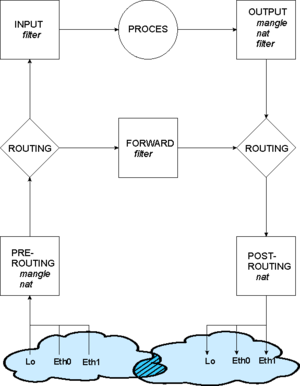
[[Image:Iptables chains.png|300px|thumb|left|iptables flowchart showing chains]] | [[Image:Iptables chains.png|300px|thumb|left|iptables flowchart showing chains]] | ||
| + | === The filter chains === | ||
| + | Basically [[iptables]] has three filters/chains | ||
| + | *INPUT : Packets from a Interface to a local process on the machine. A packet from outside to the machine. | ||
| + | *FORWARD: Packets traversing from one Interface to another Interface | ||
| + | *OUTPUT : Packets from a local process - the machine itself - to the outside world. | ||
| + | See the tables with the command | ||
| + | <pre> | ||
| + | [root@bkshost sysconfig]# iptables -L | ||
| + | Chain INPUT (policy ACCEPT) | ||
| + | target prot opt source destination | ||
| + | |||
| + | Chain FORWARD (policy ACCEPT) | ||
| + | target prot opt source destination | ||
| + | |||
| + | Chain OUTPUT (policy ACCEPT) | ||
| + | target prot opt source destination | ||
| + | </pre> | ||
| + | === The nat chains === | ||
| + | When you use the ''[[NAT_Linux|nat]]'' table or ''mangle'' tables | ||
| + | *PREROUTING : Incoming packets ''before'' Routing decision. Used fx. for Destination [[NAT_Linux|nat]] | ||
| + | *POSTROUTING: Incoming packets ''after'' Routing decision. Used fx. for Source [[NAT_Linux|nat]] | ||
| + | *OUTPUT : Packets from a local process - the machine itself - to the outside world. | ||
| + | See the tables with the command | ||
| + | <pre> | ||
| + | [root@bkshost sysconfig]# iptables -L -t nat | ||
| + | Chain PREROUTING (policy ACCEPT) | ||
| + | target prot opt source destination | ||
| + | |||
| + | Chain POSTROUTING (policy ACCEPT) | ||
| + | target prot opt source destination | ||
| + | |||
| + | Chain OUTPUT (policy ACCEPT) | ||
| + | target prot opt source destination | ||
| + | </pre> | ||
Revision as of 15:37, 7 March 2009
iptables is a packet filtering, NAT/PAT and packet mangling tool for Linux. Used by a variety of Linux distributions including Ubuntu, Redhat and CentOS. Iptables is highly configurable and are used in many firewall solutions.
Using IPTABLES
Iptables is a commandline command with numerous options, and need some training to master. There are three tables you can use filter(default) nat and mangle. Only filter and nat shown below.
The filter chains
Basically iptables has three filters/chains
- INPUT : Packets from a Interface to a local process on the machine. A packet from outside to the machine.
- FORWARD: Packets traversing from one Interface to another Interface
- OUTPUT : Packets from a local process - the machine itself - to the outside world.
See the tables with the command
[root@bkshost sysconfig]# iptables -L Chain INPUT (policy ACCEPT) target prot opt source destination Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
The nat chains
When you use the nat table or mangle tables
- PREROUTING : Incoming packets before Routing decision. Used fx. for Destination nat
- POSTROUTING: Incoming packets after Routing decision. Used fx. for Source nat
- OUTPUT : Packets from a local process - the machine itself - to the outside world.
See the tables with the command
[root@bkshost sysconfig]# iptables -L -t nat Chain PREROUTING (policy ACCEPT) target prot opt source destination Chain POSTROUTING (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination