Difference between revisions of "CCNA Explorer 3 Basic Switch Concepts and Configuration"
From Teknologisk videncenter
m |
m |
||
| Line 104: | Line 104: | ||
|- | |- | ||
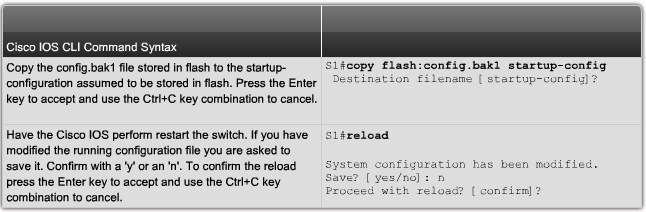
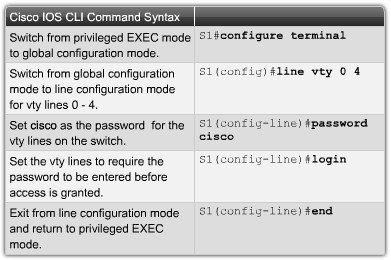
|[[Image:ScreenShot066.jpg|800px|left|thumb|EXEC mode password]] | |[[Image:ScreenShot066.jpg|800px|left|thumb|EXEC mode password]] | ||
| + | |- | ||
| + | |[[Image:ScreenShot100.jpg|800px|left|thumb|Configure encypted passwords]] | ||
| + | |- | ||
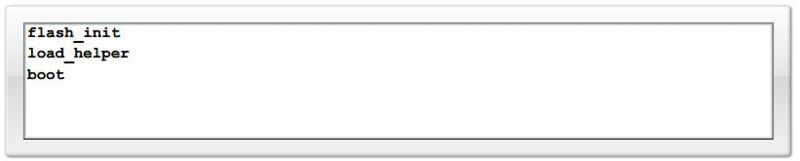
| + | |[[Image:ScreenShot001.jpg|800px|left|thumb|Password recovery]] | ||
| + | |- | ||
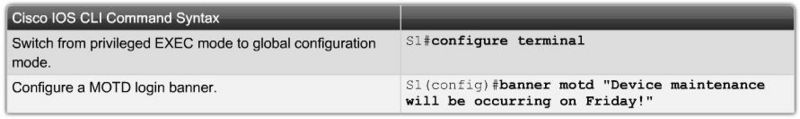
| + | |[[Image:ScreenShotNew001.jpg|800px|left|thumb|Banner login]] | ||
| + | |- | ||
| + | |[[Image:ScreenShotNew002.jpg|800px|left|thumb|Banner motd]] | ||
| + | |- | ||
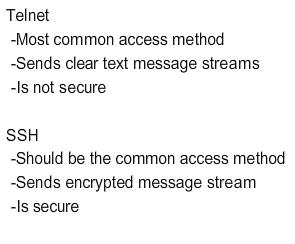
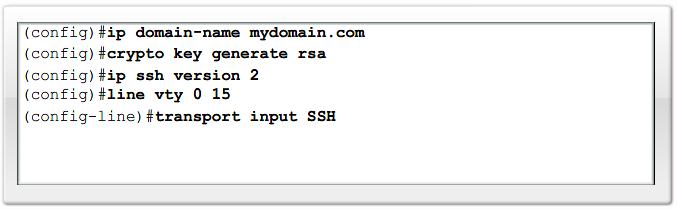
| + | |[[Image:ScreenShotNew003.jpg|800px|left|thumb|Telnet & SSH]] | ||
| + | |- | ||
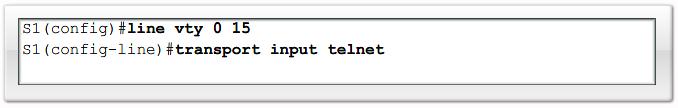
| + | |[[Image:ScreenShotNew004.jpg|800px|left|thumb|Transport input telnet]] | ||
| + | |- | ||
| + | |[[Image:ScreenShotNew005.jpg|800px|left|thumb|Transport input SSH]] | ||
|- | |- | ||
| | | | ||
| + | ==Common Security Attacks== | ||
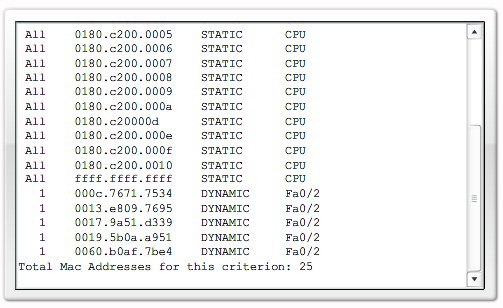
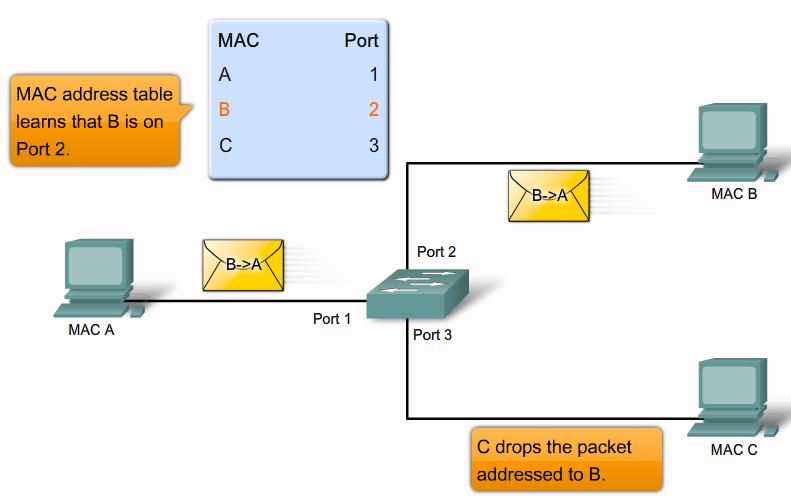
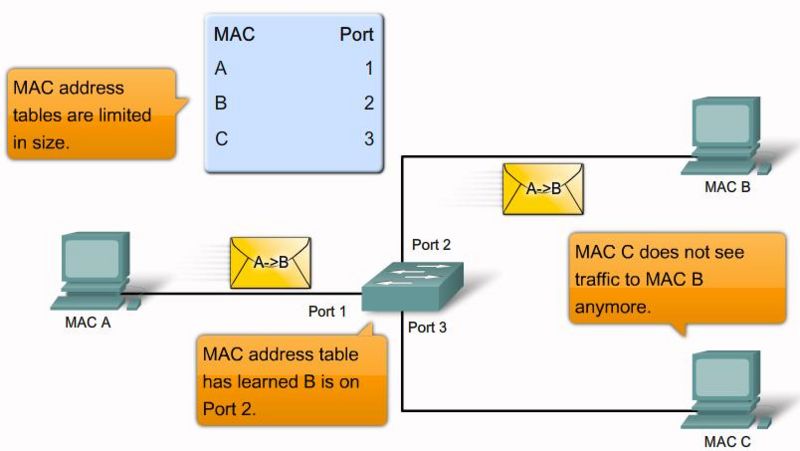
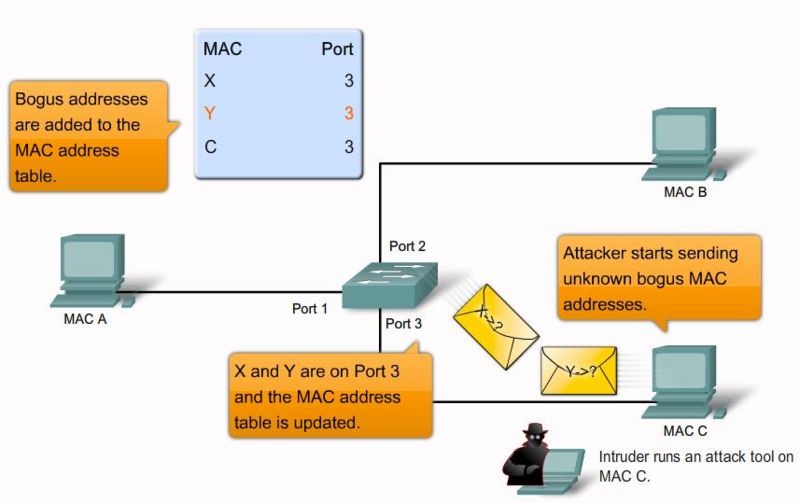
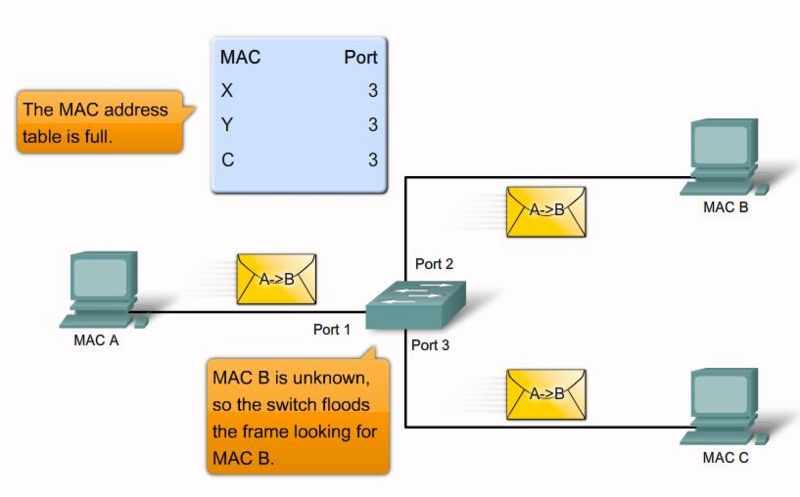
| + | ===MAC Address Flooding=== | ||
| + | {| | ||
| + | |[[Image:ScreenShotNew006.jpg|800px|left|thumb|MAC flooding attack step 1]] | ||
| + | |- | ||
| + | |[[Image:ScreenShotNew007.jpg|800px|left|thumb|MAC flooding attack step 2]] | ||
| + | |- | ||
| + | |[[Image:ScreenShotNew008.jpg|800px|left|thumb|MAC flooding attack step 3]] | ||
| + | |- | ||
| + | |[[Image:ScreenShotNew009.jpg|800px|left|thumb|MAC flooding attack step 4]] | ||
| + | |- | ||
| + | |[[Image:ScreenShotNew010.jpg|800px|left|thumb|MAC flooding attack step 5]] | ||
| + | |- | ||
| + | | | ||
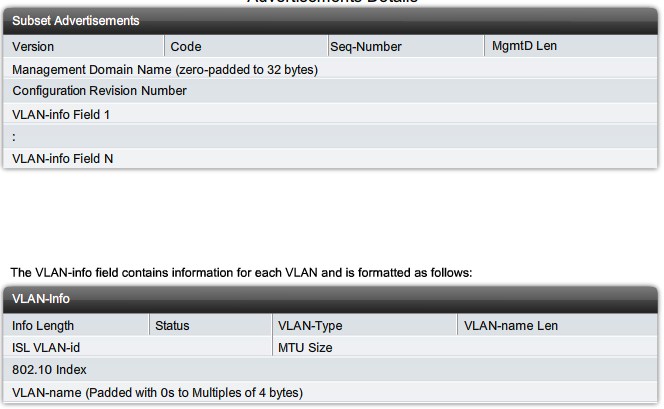
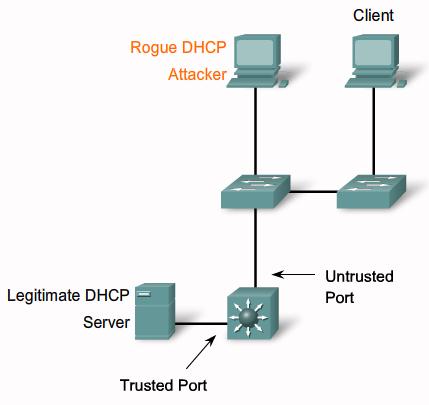
| + | ===DHCP Spoofing=== | ||
| + | {| | ||
| + | |[[Image:ScreenShotNew011.jpg|800px|left|thumb|DHCP Spoofing]] | ||
| + | |- | ||
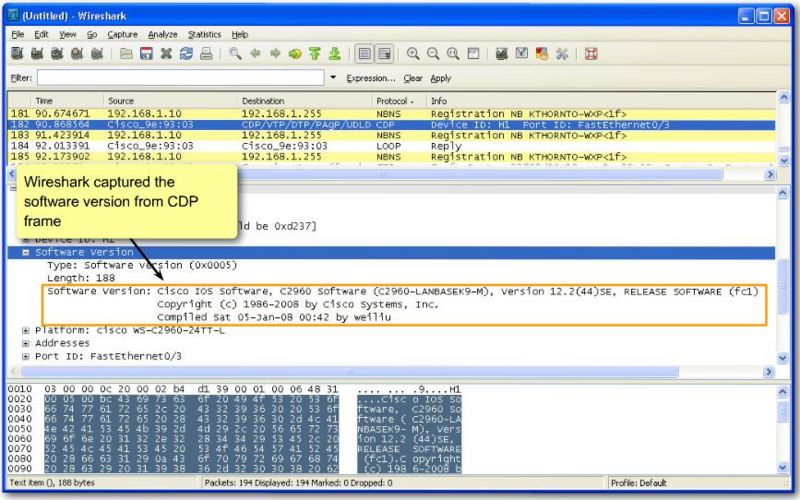
| + | |[[Image:ScreenShotNew012.jpg|800px|left|thumb|CDP Attack]] | ||
| + | |- | ||
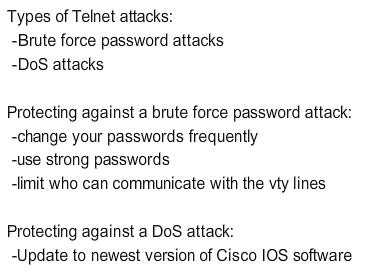
| + | |[[Image:ScreenShotNew013.jpg|800px|left|thumb|Telnet Attack]] | ||
| + | |- | ||
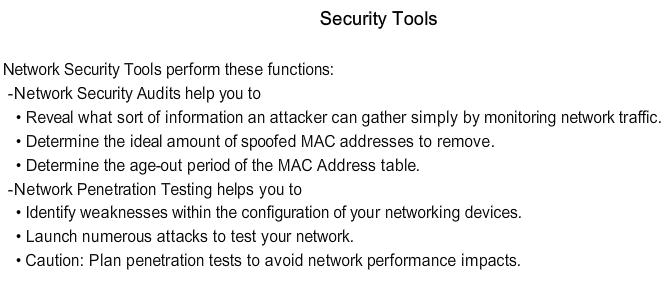
| + | |[[Image:ScreenShotNew014.jpg|800px|left|thumb|Security Tools]] | ||
| + | |- | ||
| + | |[[Image:ScreenShotNew015.jpg|800px|left|thumb|Switchport Security]] | ||
| + | |- | ||
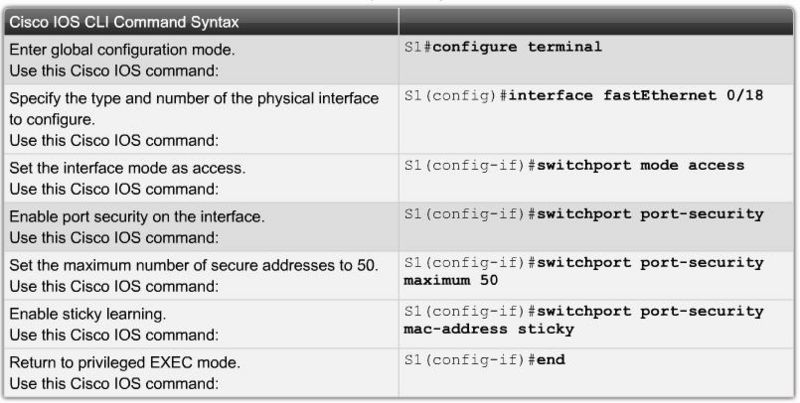
| + | |[[Image:ScreenShotNew016.jpg|800px|left|thumb|Switchport Security configuration]] | ||
| + | |- | ||
| + | |[[Image:ScreenShotNew017.jpg|800px|left|thumb|Verify port security]] | ||
| + | |- | ||
| + | |[[Image:ScreenShotNew017.jpg|800px|left|thumb|Secure Unused Ports]] | ||
| + | |- | ||
| + | | | ||
| + | |||
Kommet til 2.4.1 | Kommet til 2.4.1 | ||
Revision as of 20:22, 18 August 2010
| ||||||||||||||||||||||||||||||||||||||||||||||||||
| ||||||||||||||||||||||||||||||||||||||||||||||||||
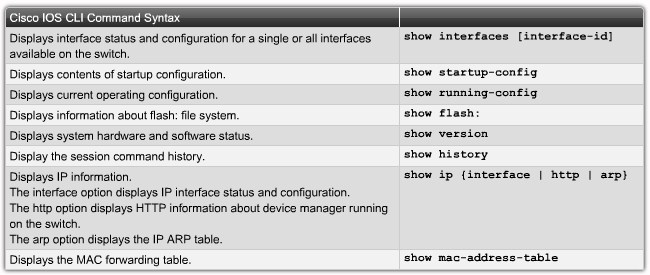
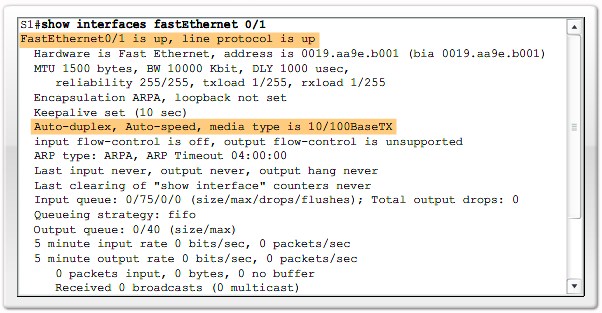
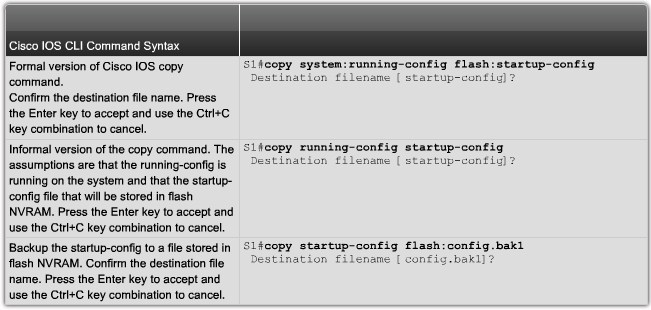
ContentsNavigating Command-Line Interfaces Modes
|